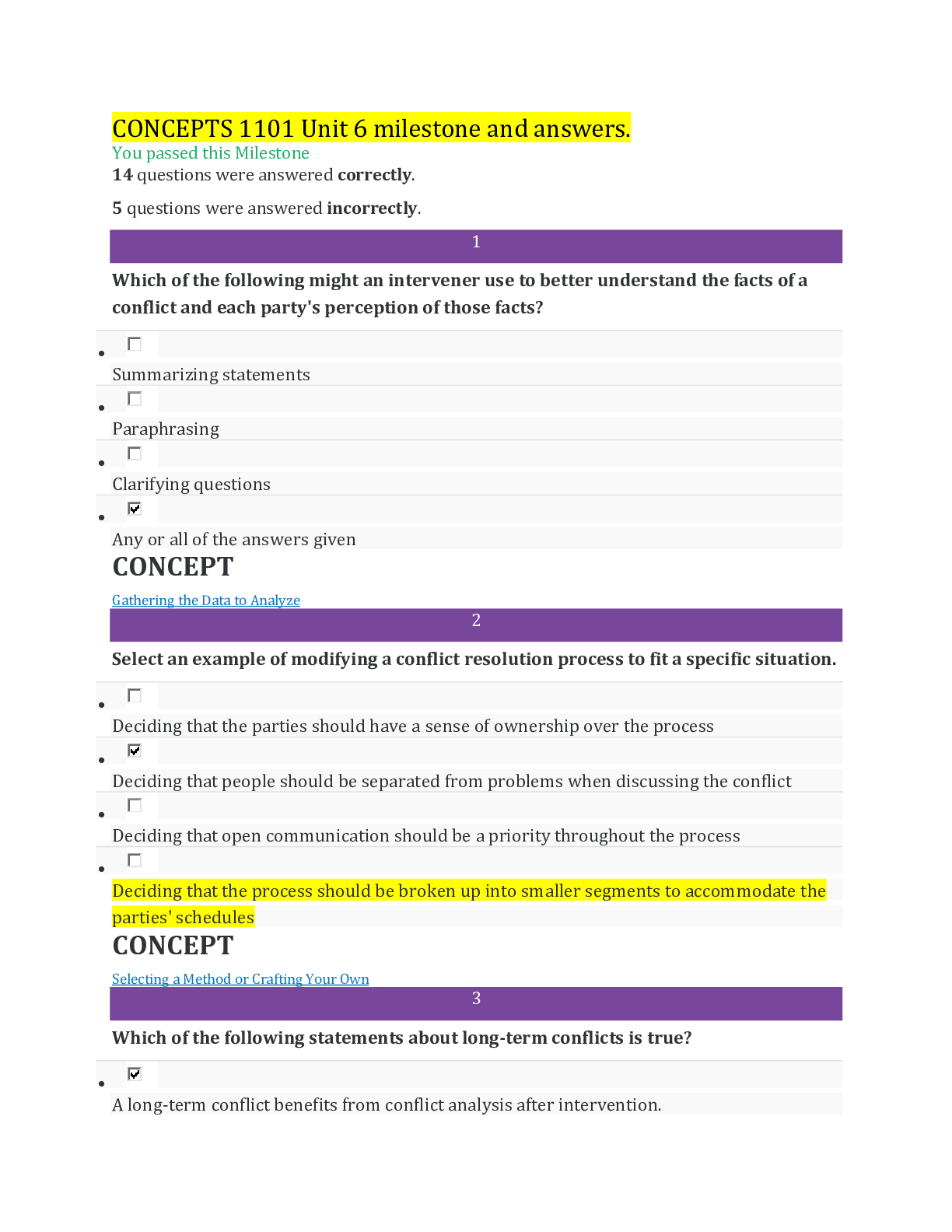
How Can An Adversary Use Information Available In Public Quizlet
How Can An Adversary Use Information Available In Public Quizlet - An adversary can use public records combined with other data sources to craft scams and target individuals. How can an adversary use information available in public records to target you? It is crucial to provide only. An opponent can utilize details found in openly accessible documents to exploit you in several ways. Department of defense (dod) cyber awareness challenge 2024 (1 hr) (pre test) how can an adversary use information available in public. Combine it with information from other. Firstly, they can merge this data with. Combine it with information from other data sources to learn how best to bait you with a scam
Firstly, they can merge this data with. An opponent can utilize details found in openly accessible documents to exploit you in several ways. An adversary can use public records combined with other data sources to craft scams and target individuals. Combine it with information from other data sources to learn how best to bait you with a scam Department of defense (dod) cyber awareness challenge 2024 (1 hr) (pre test) how can an adversary use information available in public. How can an adversary use information available in public records to target you? Combine it with information from other. It is crucial to provide only.
It is crucial to provide only. Combine it with information from other. How can an adversary use information available in public records to target you? An opponent can utilize details found in openly accessible documents to exploit you in several ways. An adversary can use public records combined with other data sources to craft scams and target individuals. Combine it with information from other data sources to learn how best to bait you with a scam Firstly, they can merge this data with. Department of defense (dod) cyber awareness challenge 2024 (1 hr) (pre test) how can an adversary use information available in public.
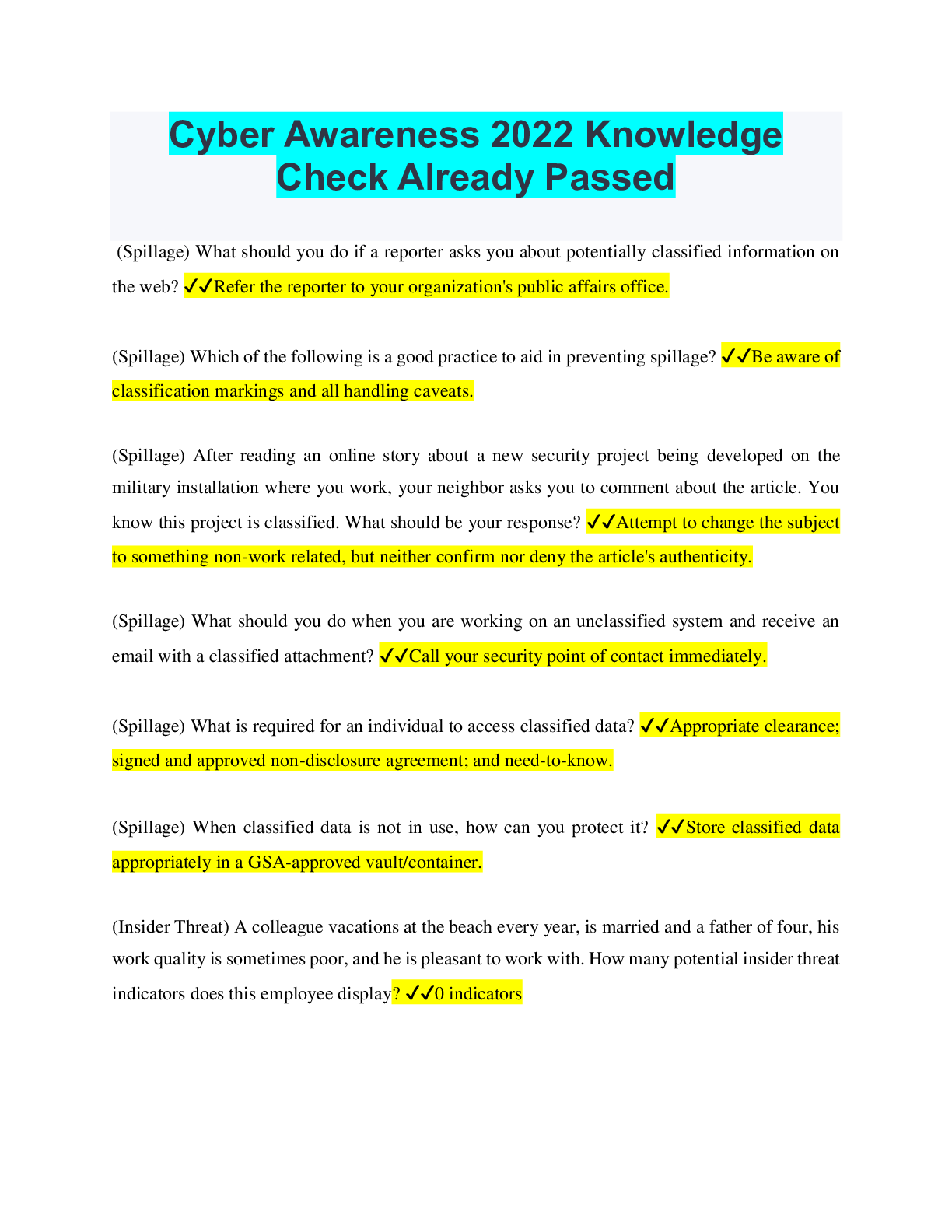
Cyber Awareness 2024 Quizlet Knowledge Check Dodi Yvonne
Combine it with information from other. An opponent can utilize details found in openly accessible documents to exploit you in several ways. An adversary can use public records combined with other data sources to craft scams and target individuals. Combine it with information from other data sources to learn how best to bait you with a scam Department of defense.
How Can an Adversary Use Information Available in Public Records to
Department of defense (dod) cyber awareness challenge 2024 (1 hr) (pre test) how can an adversary use information available in public. It is crucial to provide only. Firstly, they can merge this data with. How can an adversary use information available in public records to target you? Combine it with information from other.
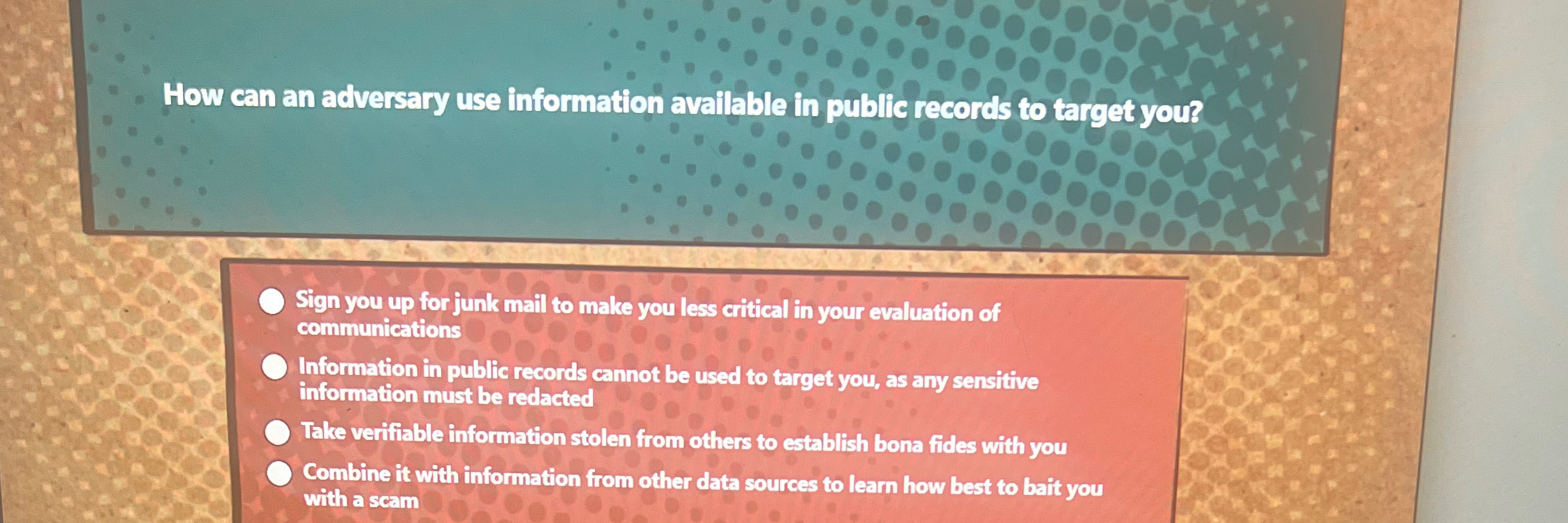
Presentation Objectives ppt download
Combine it with information from other. Combine it with information from other data sources to learn how best to bait you with a scam An opponent can utilize details found in openly accessible documents to exploit you in several ways. An adversary can use public records combined with other data sources to craft scams and target individuals. Department of defense.
Solved How can an adversary use information available in public
Firstly, they can merge this data with. How can an adversary use information available in public records to target you? An opponent can utilize details found in openly accessible documents to exploit you in several ways. Department of defense (dod) cyber awareness challenge 2024 (1 hr) (pre test) how can an adversary use information available in public. Combine it with.
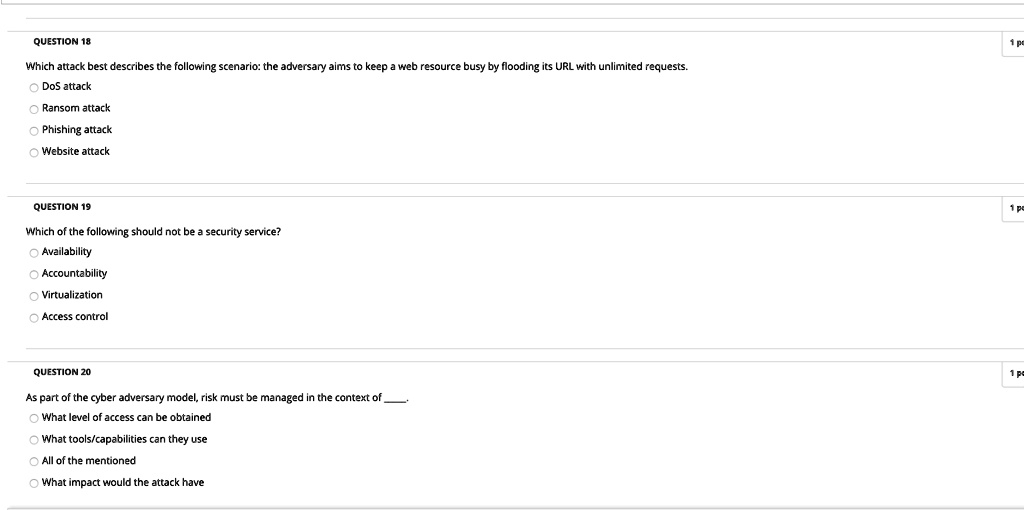
SOLVED QUESTION 18 Which attack best describes the following scenario
It is crucial to provide only. An adversary can use public records combined with other data sources to craft scams and target individuals. How can an adversary use information available in public records to target you? An opponent can utilize details found in openly accessible documents to exploit you in several ways. Department of defense (dod) cyber awareness challenge 2024.
How can an adversary use information available in public records to
Department of defense (dod) cyber awareness challenge 2024 (1 hr) (pre test) how can an adversary use information available in public. An opponent can utilize details found in openly accessible documents to exploit you in several ways. How can an adversary use information available in public records to target you? Combine it with information from other data sources to learn.
How Can An Adversary Use Information Available In Public Quizlet
Combine it with information from other. Firstly, they can merge this data with. An opponent can utilize details found in openly accessible documents to exploit you in several ways. It is crucial to provide only. An adversary can use public records combined with other data sources to craft scams and target individuals.
Cyber Awareness 2024 Quizlet Knowledge Check Dodi Yvonne
Combine it with information from other. How can an adversary use information available in public records to target you? It is crucial to provide only. Combine it with information from other data sources to learn how best to bait you with a scam Department of defense (dod) cyber awareness challenge 2024 (1 hr) (pre test) how can an adversary use.
Solved How can an adversary use information available in
An opponent can utilize details found in openly accessible documents to exploit you in several ways. An adversary can use public records combined with other data sources to craft scams and target individuals. Combine it with information from other data sources to learn how best to bait you with a scam How can an adversary use information available in public.
How Can An Adversary Use Information Available In Public Records
Combine it with information from other data sources to learn how best to bait you with a scam Combine it with information from other. An opponent can utilize details found in openly accessible documents to exploit you in several ways. Firstly, they can merge this data with. An adversary can use public records combined with other data sources to craft.
Combine It With Information From Other.
An adversary can use public records combined with other data sources to craft scams and target individuals. Firstly, they can merge this data with. Combine it with information from other data sources to learn how best to bait you with a scam An opponent can utilize details found in openly accessible documents to exploit you in several ways.
How Can An Adversary Use Information Available In Public Records To Target You?
Department of defense (dod) cyber awareness challenge 2024 (1 hr) (pre test) how can an adversary use information available in public. It is crucial to provide only.